Protecting Withdrawal Keys
Protecting withdrawal keys is a critical part of any Ethereum 2 staker's operations. This article discusses the use of withdrawal keys and how they can be secured with existing tools.
What is the withdrawal key?
A withdrawal key is an Ethereum 2 key that controls withdrawal of Ether from Ethereum 2 validators1.
Ethereum 2 keys are similar to Ethereum 1 keys in terms of their creation and use, however they are not compatible: keys created on Ethereum 1 cannot be used for Ethereum 2.
Ethereum 2 keys come in a pair of public and private keys. Note that due to the focus of this article, from here on the term "key" refers to what is often called the secret or private key; when discussing the public key this is stated explicitly.
The withdrawal key will be held by the staker: as they are the entity providing the funds, they also want to be able to retrieve the funds.
What is the withdrawal key used for?
Information from the withdrawal key is used in two situations in Ethereum 2: creating deposit transactions on Ethereum 1, and withdrawing Ether on Ethereum 2.
When creating a deposit transaction on Ethereum 1 the withdrawal public key is used to link the deposit with the withdrawal key; this is how Ethereum 2 knows which entity is allowed to withdraw Ether. The withdrawal public key is used to incorporate data in to an Ethereum staking deposit, as shown below:
 for more details) Figure 1](/images/posts/protecting-withdrawal-keys/1-UUOWCA46.png) Figure 1: Use of a withdrawal public key in the deposit process (see [this article](/posts/understanding-ethereum-staking-deposits) for more details)
Figure 1: Use of a withdrawal public key in the deposit process (see [this article](/posts/understanding-ethereum-staking-deposits) for more details)
See the linked article for additional details, however the important point is that the withdrawal public key is used as part of every deposit agreement2.
Withdrawing Ether on Ethereum 2 is as of yet undefined in terms of the specifics of the operation. However, whatever form the operation takes in the future, it will require a signature from the withdrawal key to act as authorization:
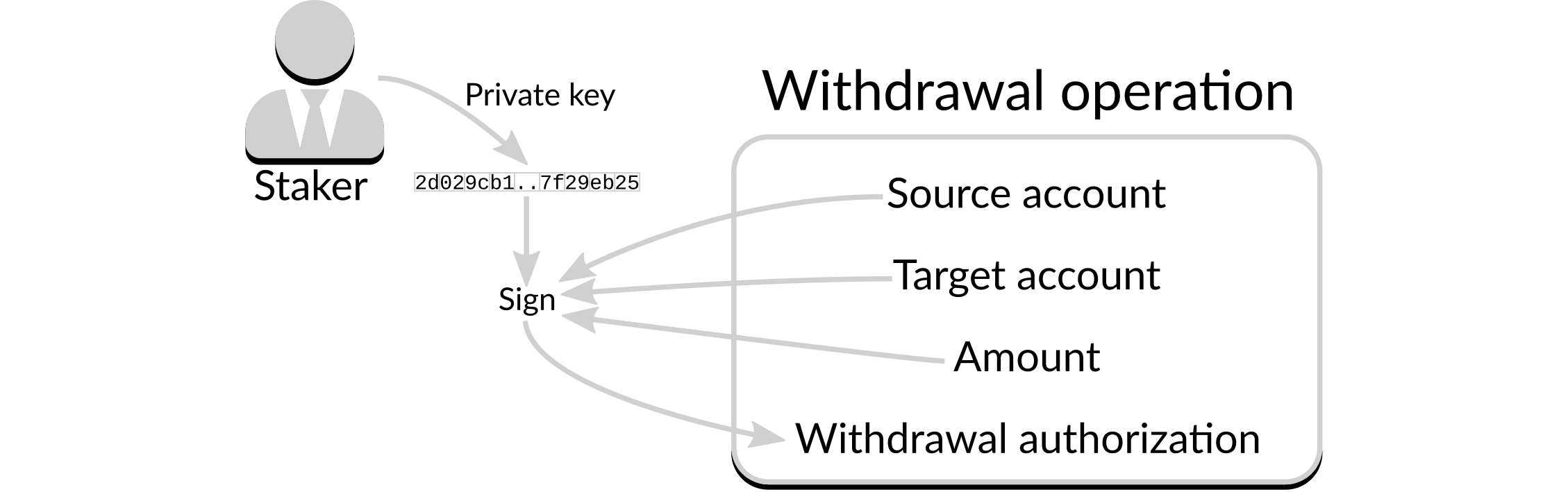 Figure 2: Outline of a withdrawal operation
Figure 2: Outline of a withdrawal operation
In the example above the withdrawal key is used by the staker to sign the details of the withdrawal operation. The Ethereum 2 network can then compare the authorization in the withdrawal operation with the withdrawal identification in the deposit agreement (as per the previous figure): if they match, the withdrawal will be able to proceed.
The withdrawal key will not be required until withdrawal operations are possible, which could easily be over a year from the time that the deposit is made. Even when withdrawals are available there is no requirement to carry them out: many stakers will be interested in rewards over the long term, so the introduction of withdrawals will therefore have little impact on their day-to-day operations.
This means that the withdrawal key should be strongly protected, with no reason to access it in the short term and only very occasional reason to access it in the long term. This implies that when balancing requirements of security and accessibility, security should be the strongest focus.
 Figure 3: Scale of security Vs. accessibility for withdrawal keys
Figure 3: Scale of security Vs. accessibility for withdrawal keys
How many keys to protect?
An outstanding question is the scope of the problem: how many withdrawal keys will there be to protect?
If you are creating a single validator then the answer is simple: one key. If you are creating more than one validator the answer is more complicated. It is possible to use a different withdrawal key for each validator, but this is not a requirement. So should each validator have a unique withdrawal key?
There are two main reasons for using multiple withdrawal keys. The first is that using the same withdrawal key for multiple validators results in them being linked: it is clear that the deposits are all owned by the same entity. From this, it is easy to calculate the funds that are accessible with that withdrawal key, and to gain information about how much Ether the entity holds. However, the use of multiple withdrawal keys is no guarantee that this information cannot be calculated by other means: the Ethereum 1 address from which deposits come, for example, provides just as much information. So, unless extreme care has been taken to date with Ethereum 1 accounts, the additional security given with multiple withdrawal keys will be minimal.
The second reason is that using the same withdrawal key makes that single key more valuable, which is more likely to result in attempts to steal the key. However, storing multiple keys in the same place leads to the same problem, so multiple keys will need to be physically or logically separated to reduce the impact of any loss.
In summary, if you want to avoid anyone being able to link multiple validators to the same entity (assuming you have separate sources for each deposit on Ethereum 1), and you have separate storage locations or protection mechanisms for each withdrawal key, then there would be a material benefit to using multiple withdrawal keys. As this is not usually the case for users, the remainder of this article discusses the use of a single withdrawal key, but note that all of the information here will also apply to multiple withdrawal keys if required.
The process
Now that the requirements are understood it is time to see how to create and protect a withdrawal key. The steps to take when creating a new withdrawal key should be:
- create the withdrawal wallet;
- create the withdrawal account;
- make a note of the withdrawal public key;
- remove the withdrawal wallet; and
- confirm the withdrawal wallet can be recovered.
Laid out graphically, the process is shown below:
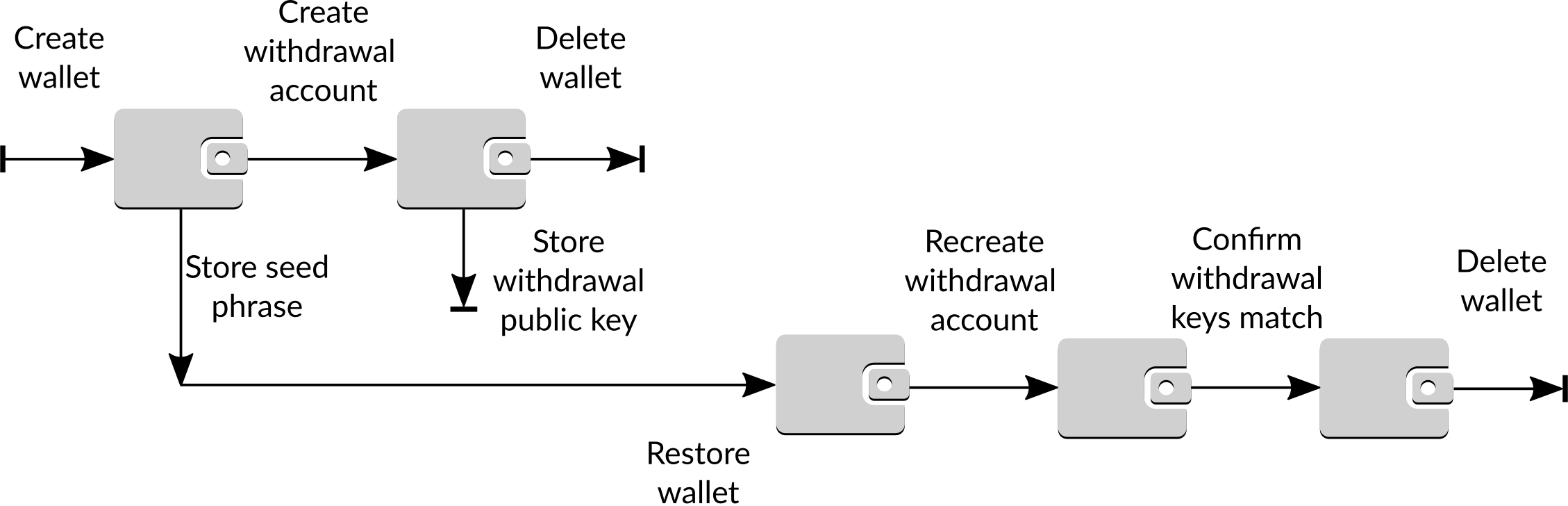 Figure 4: Process to create and protect a withdrawal key
Figure 4: Process to create and protect a withdrawal key
These steps must be run by necessity on a computer, however care should be taken to protect the computer from intrusion. A full discussion of protecting the computer is outside of the scope of this article, however at a minimum the computer should not be connected to any network while the process is being carried out.
Creating a withdrawal wallet
As of the time of writing there are no hardware wallets that support the BLS12-381 curve on which Ethereum 2 keys are based, which means that hardware wallets cannot store Ethereum 2 keys. As such, keys must be generated in software. This article uses a command-line tool called ethdo but other tools can provide similar functionality.
ethdo uses the concept of wallets. A wallet is a container for one or more accounts, and allows for the logical separation of accounts (for example, separating a withdrawal account from validating accounts). An account contains both private and public keys, as well as additional data such as a friendly name for the account so you don't have to work directly with public keys3 . To create a wallet for the withdrawal account run:
ethdo wallet create --wallet="Staking wallet" --type=hd --walletpassphrase=secret1
This creates a wallet with a mnemonic. The mnemonic is a 24-word phrase that can be used to recreate the wallet and all accounts created by it, and should be protected immediately. The mnemonic will be displayed in the output of the command, and should be stored safely offline. If the mnemonic is not displayed as part of the above command then the wallet can not be recovered and should not be used.
There are many options for protecting mnemonics, such as Blockplate and Cryptosteel, but it can be as easy as writing the words down and storing them in a safe (and preferably fire-proof) place. Bear in mind, though, that without these words you will not be able to withdraw your funds, so take whatever steps you deem appropriate.
Once your mnemonic is protected you can proceed to creating a withdrawal account.
Creating a withdrawal account
The withdrawal account is created with:
ethdo account create --account="Staking wallet/Withdrawal account" --walletpassphrase=secret1 --passphrase=secret2
The wallet passphrase is the same as you provided in the previous section. The passphrase protects just this account, and is only used briefly until the account is deleted.
Making a note of the withdrawal public key
As per its name, the withdrawal public key is public, and has no particular requirements for security. To see the public key run:
ethdo account info --account="Staking wallet/Withdrawal account"
If this does anything other than print the public key of the withdrawal account it may indicate that there is a mistake with the creation of the withdrawal account; the commands run previously should be checked carefully for errors.
Note that although the withdrawal public key is not secret, reasonable steps should be undertaken to ensure that a malicious attacker cannot swap the withdrawal public key with their own public key, wherever you store it.
Removing the withdrawal wallet
If all of the steps above have been carried out correctly it is safe to remove the withdrawal wallet. To do this run:
ethdo wallet delete --wallet="Staking wallet"
You can confirm the wallet has been deleted by attempting to access it:
ethdo wallet info --wallet="Staking wallet"
which should return an error stating the wallet could not be found.
Confirm the withdrawal wallet can be recovered
Before you use the withdrawal key for any deposits it is a very good idea to recover your withdrawal wallet. This not only ensures that you are familiar with the process, but will catch any errors that may have occurred before you trust it with funds.
The first step is to create a new wallet using the mnemonic. To do so run:
ethdo wallet create --wallet="Recovery wallet" --type=hd --walletpassphrase=temp1 --mnemonic="MNEMONIC"
Replacing mnemonic with your 24-word mnemonic.
You can then recreate the withdrawal account with:
ethdo account create --account="Recovery wallet/Withdrawal account" --walletpassphrase=temp1 --passphrase=temp2
and obtain its public key with:
ethdo account info --account="Recovery wallet/Withdrawal account"
At this point it is critical you confirm that the public key printed as the output of this command matches the one you made a note of earlier. If so, it confirms that your mnemonic is correct.
To remove the recovered wallet run:
ethdo wallet delete --wallet="Recovery wallet"
You can confirm the wallet has been deleted by attempting to access it:
ethdo wallet info --wallet="Recovery wallet"
which should return an error stating the wallet could not be found.
Does this apply to validator keys?
The use of validator keys in Ethereum 2 is very different to that of withdrawal keys, and indeed very different to most keys with which you will be familiar. The next article will look at validator keys, their use, and the challenges involved in protecting them.
Footnotes
-
There is nothing special about a withdrawal key compared to other Ethereum 2 keys; this is just the name given to it to help define its purpose. ↩
-
In fact, as shown in the diagram all that is required is the withdrawal identification. However, it is recommended the withdrawal public key is retained rather than just the withdrawal identification as it has potential additional uses (e.g. verifying signatures). ↩
-
As public keys look like
0xa9ca9cf7fa2d0ab1d5d52d2d8f79f68c50c5296bfce81546c254df68eaac0418717b2f9fc6655cbbddb145daeb282c00, this is a good thing. ↩